SSH Chat via Cloudflare Tunnel by Cloudflare Zero Trust
Build an SSH chat room with Cloudflare Tunnel

1. Intro to Cloudflare Zero Trust and Cloudflare Tunnel
- Zero Trust is a security model based on the principle of maintaining strict access controls and not trusting anyone by default, even those already inside the network perimeter. Ref: Zero Trust security
- Cloudflare Zero Trust (i) Eliminate implicit trust while providing consistent experiences for remote and office users alike; (ii) Secure access, defend against threats, and secure with Microsoft and other SaaS tools; (iii) Tackle your Zero Trust journey one step at a time with composable, in-line security services. Ref: Cloudflare Zero Trust Platform
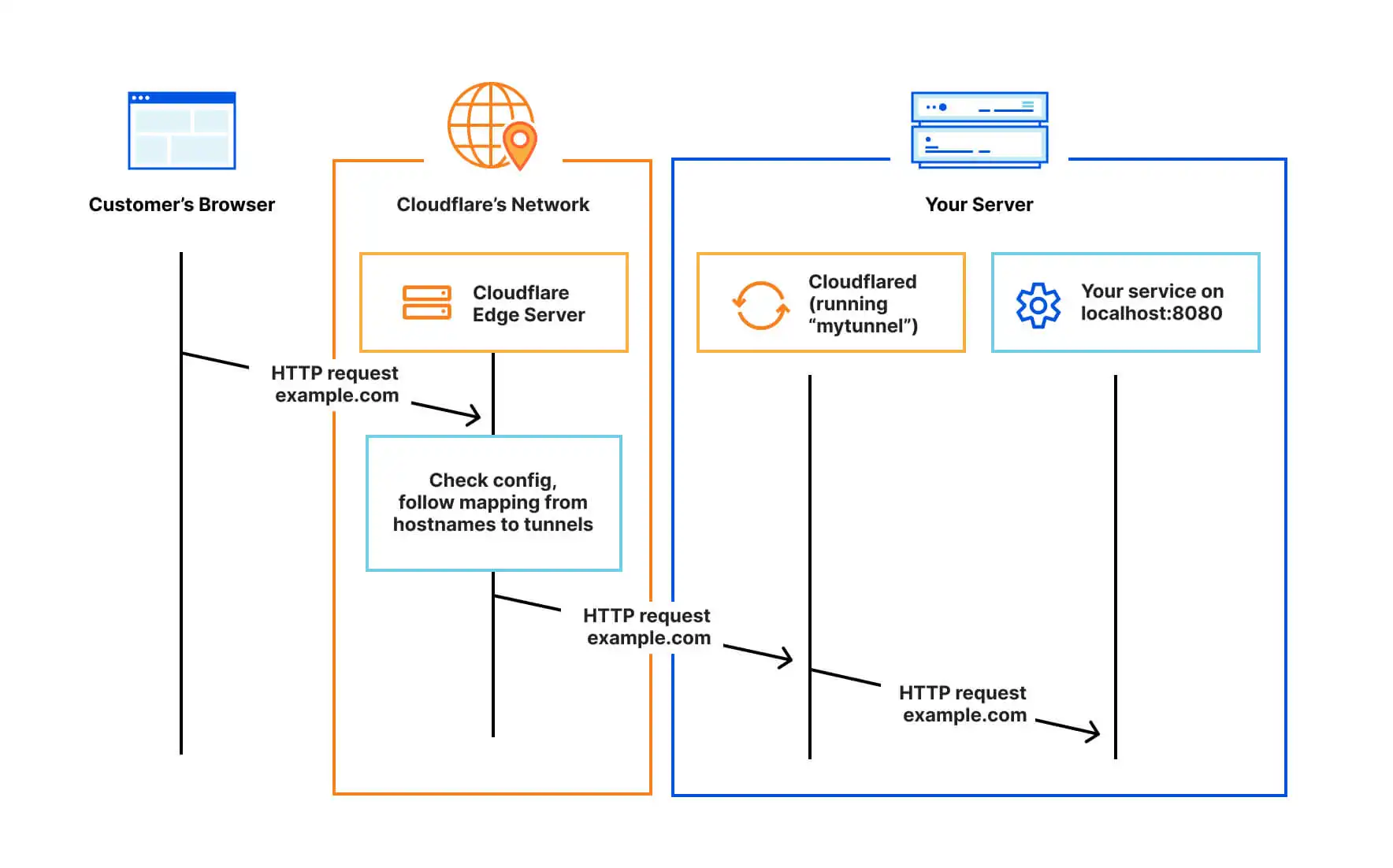
- Cloudflare Tunnel Cloudflare Tunnel provides you with a secure way to connect your resources to Cloudflare without a publicly routable IP address. With Tunnel, you do not send traffic to an external IP — instead, a lightweight daemon in your infrastructure (cloudflared) creates outbound-only connections to Cloudflare’s global network. Cloudflare Tunnel can connect HTTP web servers, SSH servers, remote desktops, and other protocols safely to Cloudflare. This way, your origins can serve traffic through Cloudflare without being vulnerable to attacks that bypass Cloudflare. Ref: Cloudflare Tunnel
- To put it simpler, it looks like the figure below:
2. Intro to SSH Chat
SSH-Chat is a custom SSH server written in Golang. When users log in to this SSH, they will get an online chat room in the terminal (instead of a shell environment). It will not conflict with your server's normal login SSH, the main features are:
- Access chat rooms via SSH
- Users can send private messages to each other, and hide/only display messages from specific users
- Support whitelist/blacklist
- set color theme
- Admins can kick out unfriendly users
- Add a timestamp prefix to the message
- Identity can be confirmed via the user's SSH public key
Official repo: ssh-chat
3. SSH Chat Configuration
- Prerequisite
apt -y update
apt -y install curl nginx python3-certbot-nginx
curl -fsSL https://get.docker.com -o get-docker.sh
sh get-docker.sh
- Clone repo
cd /your/path
mkdir sshchat && cd sshchat
git clone https://github.com/shazow/ssh-chat.git
- Build Docker image with tag
docker build -t sshchat-app:latest .
- Modify compose file
nano docker-compose.yml
version: '3.8'
services:
app:
container_name: ssh-chat
# build: .
image: sshchat-app:latest
ports:
- 127.0.0.1:40001:2022
restart: unless-stopped
volumes:
- type: bind
source: ~/.ssh/ # You can specify other user(s) on your server too
target: /root/.ssh/
read_only: true
- Bring up the container
docker compose up -d
4. Cloudflare Configuration
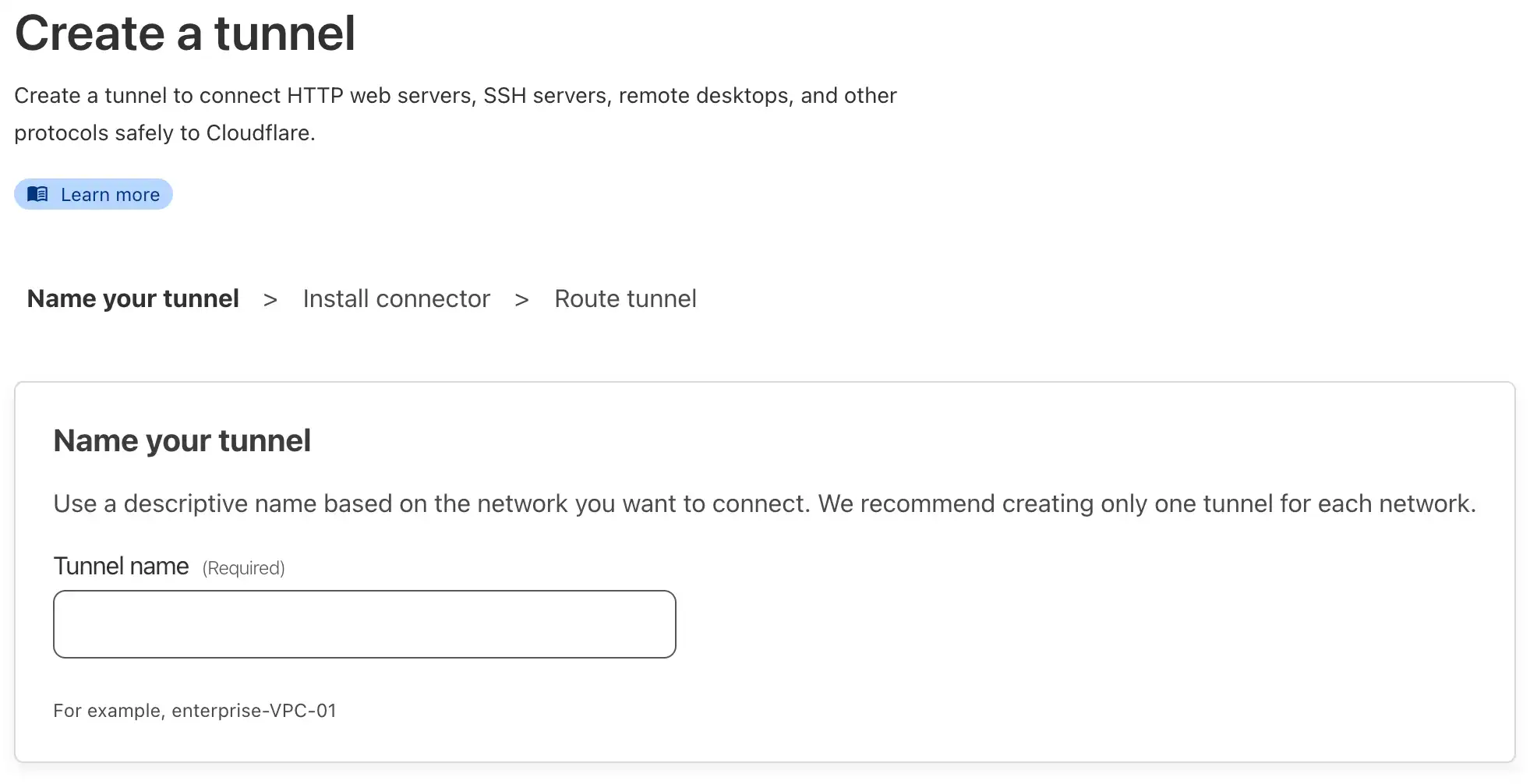
- Log in to the Cloudflare Zero Trust console, select the
Accessmenu in the left navigation bar, enter the Tunnels configuration, clickCreate a tunnelto create a Tunnel, and enter the Tunnel tunnel name.
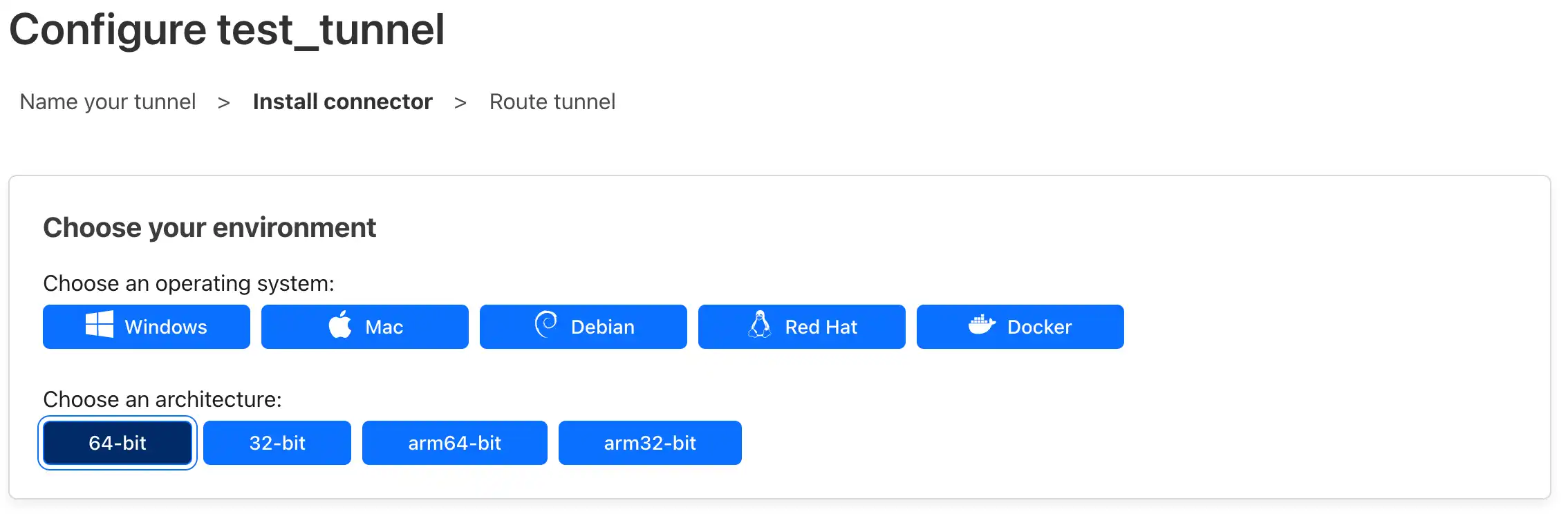
- Select the server's operating system and platform architecture
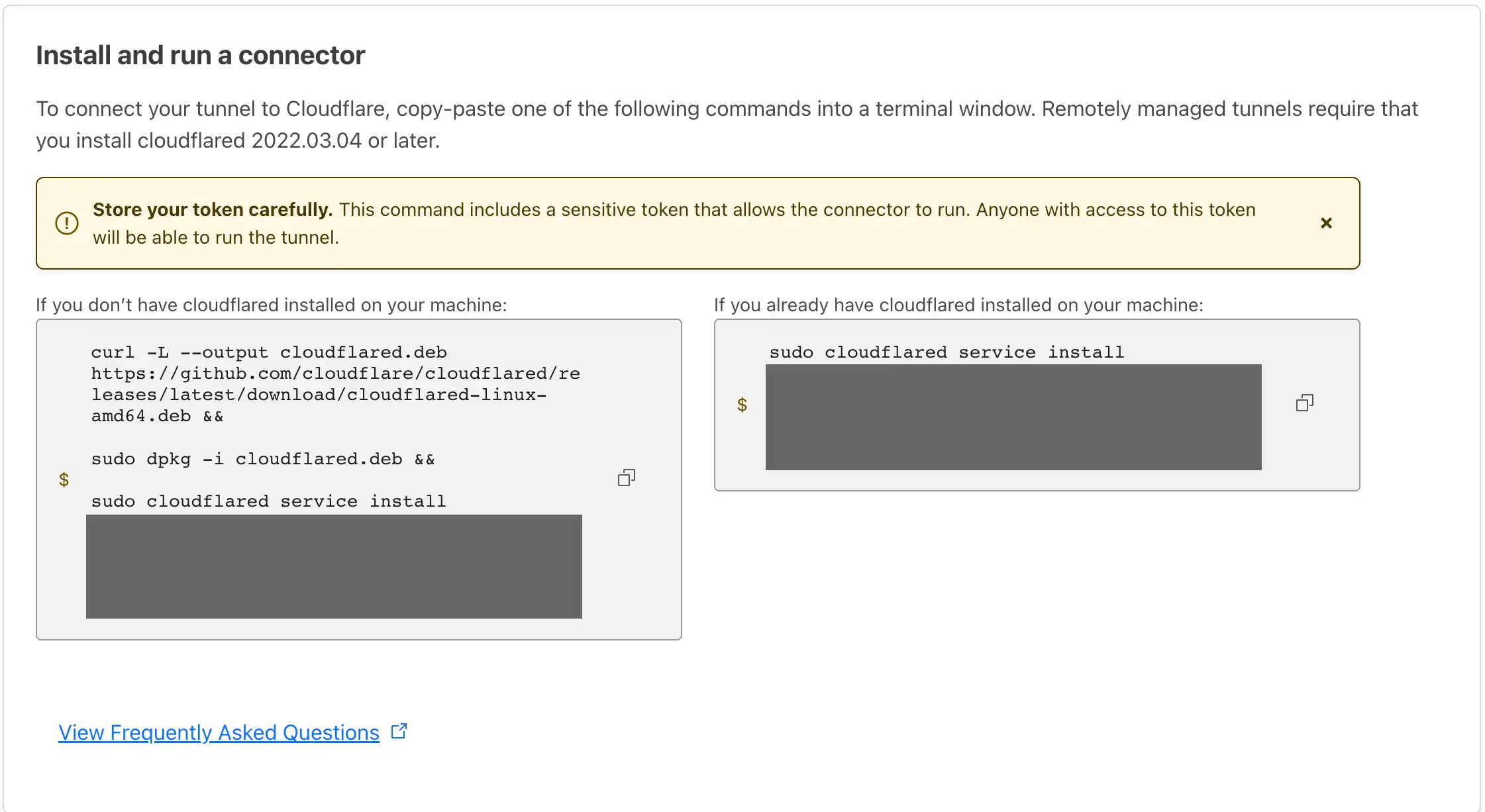
- Copy the command on the left and paste it into the SSH session to install Cloudflared (be careful not to leak the Token)
- Now that the Cloudflared service has been installed on the server. Next we will configure the Cloudflared listening service, as below:
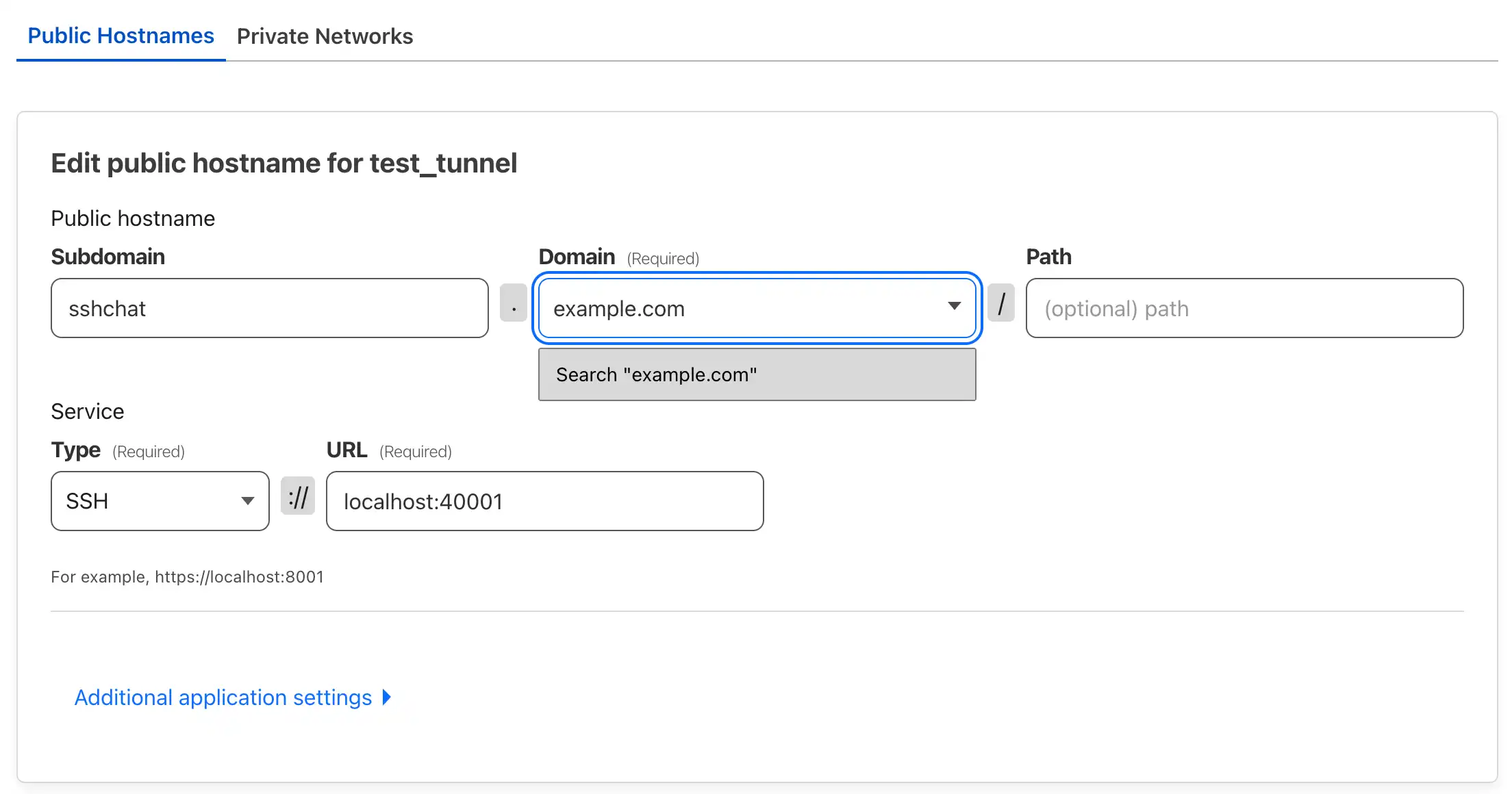
- Click Save, and Cloudflare will automatically add a DNS resolution record to the hosted domain name. Now open your domain name and you can have a pleasant visit.
As long as it is a device that can install Cloudflared and can access the Cloudflare network, you can use Cloudflare Tunnel to protect the access to the service.
Cloudflare Tunnel can be used for intranet penetration, reverse proxy, and fully automatic HTTPS, supporting protocols such as HTTP, HTTPS, TCP, UNIX, SSH, RDP, SMB, UNIX+TLS, etc.
5. Local Cloudflare Setup
Here local means your personal device.
Since we will not expose the port of SSH Chat to the public network, friends who want to join the chat room need to install Cloudflared on their personal computers and add an SSH configuration (it will not affect other SSH configurations), taking macOS as an example:
- Install Cloudflared
brew install cloudflared
- Check Cloudflared path
which cloudflared
It will have an output showing your Cloudflared path such as:
/usr/local/bin/cloudflared
- Edit your local SSH configurations
nano ~/.ssh/config
Add the following configuration (take the SSH Chat we just brought up as an example)
Host sshchat.example.com
ProxyCommand /usr/local/bin/cloudflared access ssh --hostname %h
(i) Replace sshchat.example.com with your own deployed hostname
(ii) Replace /usr/local/bin/cloudflared with the path to Cloudflared on your mac
- Now you can access the SSH Chat via:
ssh sshchat.example.com
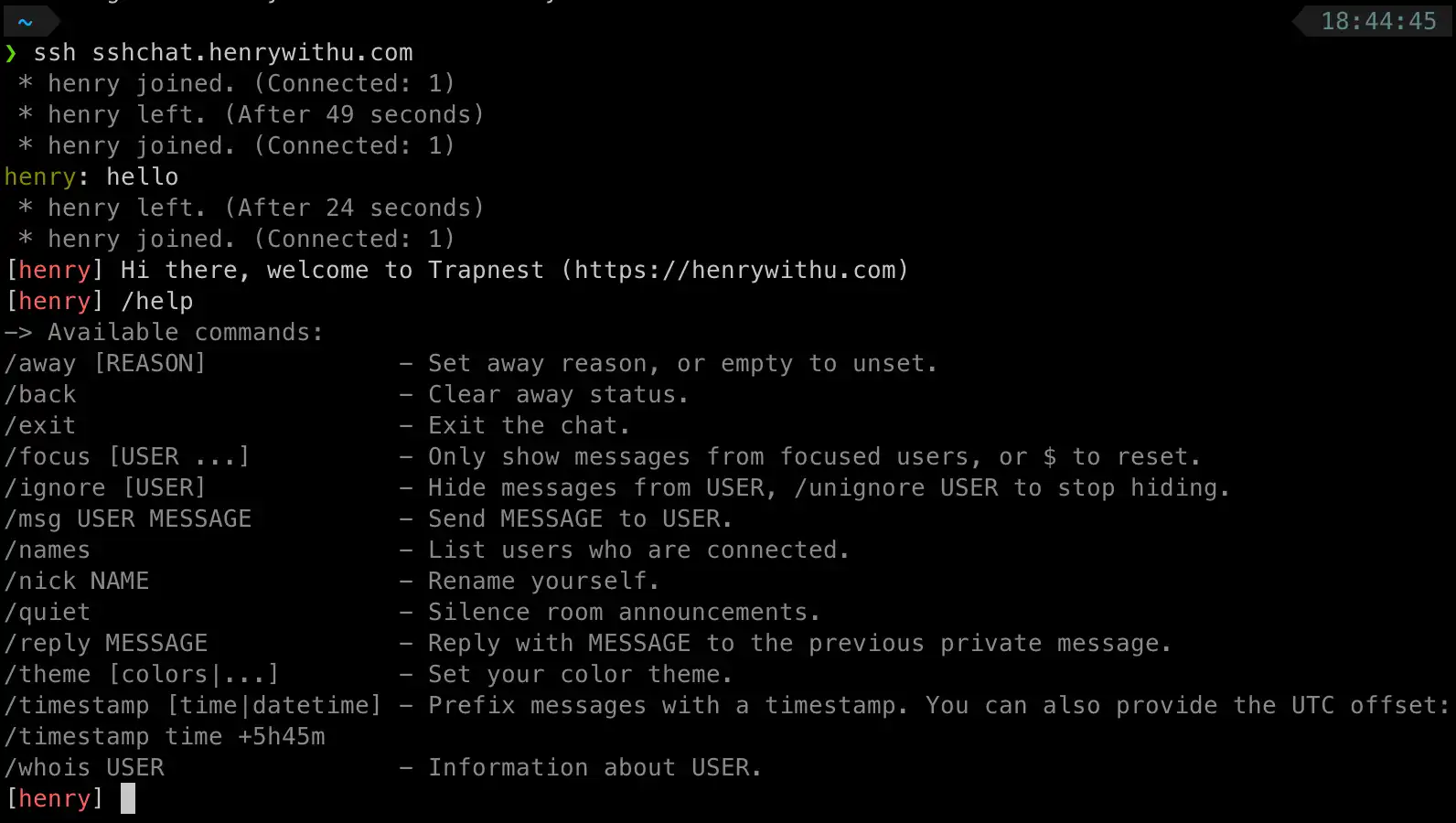
Enjoy!
If you have any question or suggestion, feel free to leave a comment, or contact me by email [email protected]
Copyright statement: Unless otherwise stated, all articles on this blog adopt the CC BY-NC-SA 4.0 license agreement. For non-commercial reprints and citations, please indicate the author: Henry, and original article URL. For commercial reprints, please contact the author for authorization.
